Scariestthingieversaw.com
From Super8
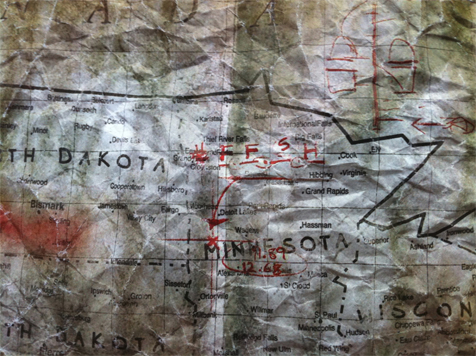
(→Dec. 28, 2010: New image - A Map) |
(→Dec. 28, 2010: New image - A Map) |
||
| Line 520: | Line 520: | ||
[[File:STIESMap.JPG]] | [[File:STIESMap.JPG]] | ||
| + | |||
| + | *A symbol and the letters FFSH can be read | ||
| + | *The numbers 11.89 and 12.68 also appear | ||
| + | *A hand drawn diagram of arches and squares | ||
| + | *This pointed to a staircase and windows at the Fergus Falls State Hospital (FFSH) | ||
| + | Link to original staircase picture: http://pics.livejournal.com/laurapalmer813/pic/002awrra.jpg | ||
== MISC. - OOG == | == MISC. - OOG == | ||
Revision as of 02:17, 10 February 2011
ScariestThingIEverSaw.com
- Direct link: http://scariestthingieversaw.com
Discovery
- May 6th 2010, after analyzing the bootlegged teaser trailer, the words "scariest thing i ever saw" were found at the trailing end of the film reel, leading to the website.
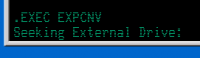
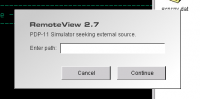
Console
On loading the website, the RemoteView interface begins booting.
May 7, 2010
|
Notes from console content below:
------------------------------------------------------------
PDP-11 Simulator
License 1130-A23R-12TR-2090
------------------------------------------------------------
Copyright 1977, DAC, Acton, Mass.
THIS SOFTWARE IS FURNISHED TO A PURCHASER UNDER A LICENSE FOR
USE ON A SINGLE COMPUTER SYSTEM AND CAN BE COPIED ONLY FOR USE
IN SUCH SYSTEM, EXCEPT AS MAY OTHERWISE BE PROVIDED IN WRITING
BY DAC OF ACTON, MASS. U.S.A.
VERSION 05.5
D. MORRIS 05-FEB-77
PERFORM PRELIMINARY SYSTEM CONFIGURATION
SET CPU 128K
SHOW CPU IOSPACE
DXMNSJ.SYS
SWAP.SYS
STARTS.COM
D 56=5015
SET TT:NOSCOPE
D 56=0
R TIMDAT
------------------------------------------------------------
STALOG AF
Secure File Structure
------------------------------------------------------------
.BOOT DX1:DXMNSJ.SYS
RUN $EXEC
Continue Y/N?
------------------------------------------------------------
STALOG AF
------------------------------------------------------------
------------------------------------------------------------
RUN $LINK
*MAIN=MAIN,SUBR/S
*+Z
Continue Y/N?
RUN $LINK2F
*PROG=MAIN,MACSUB/F
*+Z
Continue Y/N?
------------------------------------------------------------
STALOG ACCESS
------------------------------------------------------------
.UNPROTECT/SYSTEM *.*
DK:SWAP.SYS
DK:RT11AI.SYS
DK:RT11PI.SYS
DK:RT11BL.SYS
CRSCT: .BLKW 10.
CRVSC: .BLKW 1
LOADNM: .RADSR /$LOAD/
MODN .BLKW 1
LCLSYM: .BLKW 8.
SRCPF: .BLKW 1
SRVSG: .BLKW 1
SYDEF: .BLKW 1
SYENT: .BLKW 1
SYFLG: .BLKW 1
.PSECT
Press any key to continue...
------------------------------------------------------------
8955655DD XST a3 FILE LIBRARY
------------------------------------------------------------
RUN $EXEC
TU56 dual DECtape drive
System Now Loading External Data
[1] Previously accessed
[2] Previously accessed
[3] Accessing File List B4 - ###### of 134640 Bytes Loaded
[]
[]
[]
[]
[]
[]
[]
[]
[]
[]
[]
[]
[]
[]
[]
[]
[]
------------------------------------------------------------
Execute - E [] Commit To Tape Drive - C [] Print - P []
------------------------------------------------------------
References to note:
Analyzing the source: |
May 13, 2010
|
With the file completely downloaded, the RemoteView terminal continued to display the following text: ------------------------------------------------------------ AF FILE LIBRARY ------------------------------------------------------------ Sector 9909 [] DD09 Extract [] CL03 Transmission [] CL05 Extract [] CL56 Token [] ------------------------------------------------------------ The terminal then prompts the user to re-connect
Once updates completed, the file load text changed. New options became available.
---------------------------------------------------------------------------------------------
Execute - .EXEC [] Commit To Tape Drive - .COMT [] Print - .PRINT [] Reenter - .REENTER
---------------------------------------------------------------------------------------------
fd = open ("DEV1:", O_WRONLY);
status = ioctl (fd, FIODISKINIT, 0);
struct stat statStruct;
fd = open ("AF-B4.01", O_RDONLY);
status = ioctl (fd, FIOFSTATGET, &statStruct);
---------------------------------------------------------------------------------------------
AF-B4.01
---------------------------------------------------------------------------------------------
AF-B4.01 DIR
Sorted by: type
Volume ID: DD1
Owner :
A5RSR .BAS 11
A5RST .BAS 15
RSCOM8 .DAT 13
A5RSR1 .WRK 5
CL03 .WRK 2
DD09 .WRK 2
GRMF55 .WRK 5
FATR7 .WRK 3
FATR8 .WRK 8
GMRF36 .TXT 5
GMRF71 .TXT 4
---------------------------------------------------------------------------------------------
Execute - .EXEC [] Commit To Tape Drive - .COMT [] Print - .PRINT [] Reenter - .REENTER
---------------------------------------------------------------------------------------------
.PRINT RSCOM8
no certainty if a live may be after us we go underground
.REENTER
------------------------------------------------------------ PDP-11 Simulator License 1130-A23R-12TR-2090 ------------------------------------------------------------ MOUNT Continue Y/N? Y DEVICE?
?IND-F-Invalid Request
| (images) |
June 1, 2010
A5RSR .BAS 11 A5RST .BAS 15 RSCOM8 .DAT 13 EXPCNV .DAT 4 A5RSR1 .WRK 5 CL03 .WRK 2 DD09 .WRK 2 GRMF55 .WRK 5 FATR7 .WRK 3 FATR8 .WRK 8 GMRF36 .TXT 5 GMRF71 .TXT 4
.EXEC EXPCNV
| |||||
June 21, 2010
|
|
- The AF-B4.01 directory command prompt now interprets keys 0, 1, and 2 as enter, Y, and N, respectively. This breaks the ability to enter certain commands. (This "feature" previously existed on every prompt prior to the May 13th update.)
July 28, 2010
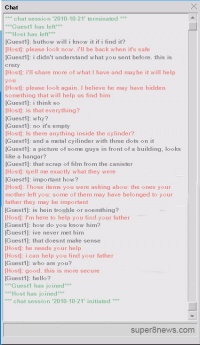
New message on printout reads: If you're who I think you are, it's about your father. I'll tell you more when I can, but you must take down those sale listings. Anything you found may be important. > I've been quiet. PLEASE - what is this about??
September 9, 2010
|